
DECODE is the premier cyber security conference in the Philippines hosted by Trend Micro. It aims to decode to local technology professionals the up-to-date information about the threat landscape, industry trends, and new technologies in order to empower them to secure the digital infrastructures of their organizations, as well as to inspire them to embark on a continuous learning journey.
To be secure is to be smart, but in today’s increasingly hyperconnected world, it may be easier said than done. More connected devices means more data to handle, interpret, manage, and secure. And while machine learning, artificial intelligence, and other new and emerging technologies may equip IT professionals in their day-to-day tasks, cybercriminals and threat actors are taking advantage of these same trends in the computing landscape for their own malicious intent.
Organizations need to empower their greatest cyber defenders. Beyond the right tools and skills to do their jobs to the best of their abilities, these experts need collaborative intelligence in order to collectively discuss issues and challenges, and share and implement best practices and strategies to detect, analyze, and respond to ever-evolving cybersecurity threats.

Trend Micro
Martin Roesler, Senior Director Forward Looking Threat Research has been with Trend Micro since 2002. Directly reporting to the CTO Rösler covers research on technology and latest Internet threats. For the past ten years he has been the head of the Forward looking Threat Research Team of Trend Micro. In charge of underground research, eCrime investigation services and global law enforcement collaboration, his team was involved in multiple successful take down and arrest activities against cyber criminals with different police units around the globe (including Japan, EMEA and North America). Before that, Rösler was head of Trend Micro's global technical support operation and the regional Trend labs. He holds a Dipl-Ing.(FH) degree in civil engineering and is working in computer security since around 1990 when he operated the “Virus Help Munich” FIDO BBS and moderated the VIRUS.GER newsgroup.

Andrew MacPherson ( @AndrewMohawk ) has been around the information security space and specifically dealing with OSInt and data graphing for more than a decade, from bypassing physical security to looking at new ways to represent data more intelligently. Previously working as the first employee at Paterva, the company that brought you Maltego, he gave valuable insights into future directions, features and solutions that could be achieved with the tool. He also was responsible for building many of the various servers that are used to integrate with it. He has also presented many novel talks at many different security conferences including Blackhat, Defcon, Hack in the Box and BSides to name a few. Outside of that he has a keen knowledge of cat memes, makes a mean cup of tea and has an avid interest in hardware
 From Breach to Bust: A Short Story of Graphing and Grey Data
From Breach to Bust: A Short Story of Graphing and Grey Data

The OSInt and Recon community have come alive in the last few years with a myriad of different tools, scripts as well as other resources for gathering and attributing information. Typically these involve single steps; from things like taking an email address to a social profile or looking up websites related to a domain. Single order tools are awesome, but using them in conjunction with various graphing methods and other tools allows you to visualise the data far beyond one order for even more awesomeness. In this section we will discuss the various methods of layout and visualisation as well as look at an example of footprinting an organisation - such as a three letter agency ;) The talk will then focus on the "OS" part of OSINT. It will go into whether breaches, forum dumps and compromised databases should be part of an investigator’s arsenal. These sources of information are usually in the grey area of obtainability and accessibility. We will discuss the level of availability of these datasets as well as practical methods to interrogate such enormous data stores. This data offers a lot more information than can be seen at first glance, its not all about which email addresses and domains were seen in Ashley Madison! Finally the talk will conclude with a demonstration showing that linking public open source data can give us valuable leads into breached data to allow us insight not commonly seen before. Think finding the private social media profiles of an individual who works at an agency. Or even how we can quickly use infrastructure based information (such as IPs/Netblocks) to not only see what people who work somewhere are interested in but also where they might have been in breached data that we would not have previously known about!

Politecnico di Milano
Stefano Zanero is an associate professor at Politecnico di Milano. His research focuses on malware analysis, cyberphysical security, and cybersecurity in general. He has an extensive speaking and teaching experience in Italy and abroad. He co-authored over 90 scientific papers and books. He is a Senior Member of the IEEE, the IEEE Computer Society (for which he is a member of the Board of Governors), and a lifetime senior member of the ACM. Stefano is also a co-founder and chairman of Secure Network, a leading information security consulting firm based in Milan and in London, and a co-founder of BankSealer, a startup in the FinTech sector that addresses fraud detection through machine learning techniques
 Securing Cyber-physical Systems: Moving Beyond Fear
Securing Cyber-physical Systems: Moving Beyond Fear
Cyber-physical systems are attracting a lot of attention: attacks on connected cars received a lot of media exposure, as did attacks on industrial control systems, medical devices, and more generally on IoT devices. A lot of this interest is driven by vulnerability research (often in the form of "stunt hacking"). While useful and frankly engaging and attractive, this research does not really help answer the fundamental question of how to embed security analysis in design. In this talk, we will use automotive security as a case study to try to outline a risk-based design methodology that can be used to deal with our hyper-connected future.

Maybank Philippines and New York
Philip is a seasoned cyber security executive with more than 20 years of experience. He is currently the Vice President and Chief Information Security Officer of both Maybank Philippines and New York. Prior to Maybank, he held cyber security leadership positions in global and local financial services institutions. He was also a cyber security consultant for various private and government corporations. He completed his undergraduate and graduate degrees in computer science from De La Salle University. He is also the first Certified Information Systems Security Professional (CISSP) in the Philippines (since year 2002). He obtained other professional certifications such as Certified Information Security Manager (2005) and Certified in Risk and Information Systems Control (2011).
 Securing Cyber-physical Systems: Moving Beyond Fear
Securing Cyber-physical Systems: Moving Beyond Fear
This talk will cover key and current cybersecurity concerns of Financial Services Institutions from the perspective of a CISO. Aside from technical concerns, the people and process aspects will also be discussed. It will also highlight strategic measures that information security officers should take to manage these cybsersecurity risks.

Interpol
Marcelo Fortes is a Digital Crime Officer working on the Strategy & Outreach team on the INTERPOL Cybercrime Directorate. He is a seconded police officer from Brazilian Federal Police with over 19 year of experience in the police force, in the field of forensic, operations planning and managing units. Marcelo holds a Master’s degree in Public Administration from Getúlio Vargas Foundation, a Specialization in Management of Public Security by National Police Academy and a Bachelor’s in Computer Science from Federal University of Santa Maria.
 A Global Effort to Fight Cybercrime
A Global Effort to Fight Cybercrime
Cybercrime is transnational in nature, with a high capacity to affect many countries around the world, forcing law enforcement agencies to reshape the path of international cooperation. The presentation shows how INTERPOL enhances its Global Strategy to help member countries fight cybercrime by always welcoming new partners to support the Cyber Programme to work collectively to ensure that the police have the ability to effectively combat cybercrime and improve digital security for all citizens. New actors work with INTERPOL and improve the effectiveness of results by harmonizing national responses, increasing interoperability and building capacity to analyze threats and share information.

Trend Micro
Jay Yaneza currently leads the global operations of Trend Micro's Managed Detection and Response (MDR) Service, and is a Cyber Threat Researcher within Trend Micro's Cyber Safety Solutions (CSS) Team. Having started his career with Trend Micro well over 16 years ago, he had developed the thirst to hunt for internet badness by analyzing threats and classifying its indicators. He initially started his career by helping Trend Micro's customers install, deploy, configure, manage and troubleshoot various Trend Micro products. Eventually, this lead to helping numerous organizations across the globe deal with malware incidents, outbreaks, as well as targeted attack incidents. His days are filled with ensuring that Trend Micro MDR customers can sleep well and, as a researcher, currently enjoys analyzing attack data and threat event correlation. Whenever he finds spare time, he works on integrating more internet-of-things (IOT) devices to make his home smarter.
 When Less is Really More: Integrated Intelligence When Analyzing Threats
When Less is Really More: Integrated Intelligence When Analyzing Threats
The amount of threat indicators that a SOC Security Analysts need to identify is magnified by the amount of data they have to sift through to make a determination of malicious activities. Security teams, in general, are now left to determine past events and are very far behind in trying to determine the future. The use of Threat Intelligence (TI) is growing in popularity, but its usefulness and applicability is always a question. Most organizations are still struggling to ingest Threat Intelligence, but is in fact more of a necessity nowadays than a luxury. In this talk, we would go through a typical Security Operations Center (SOC) process, incorporate the usefulness of running an integrated SOC and transforming it into a threat intelligence engine that would hopefully improve an organization's security posture. At the end of this session, the attendee should have an idea how to transform their existing processes, minimize using threat portals (and browser tabs), and instead gain more insight with the use of comprehensive integration.
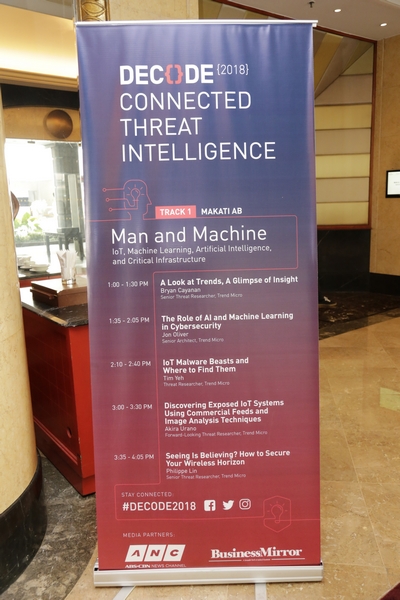
IoT, Machine Learning, Artificial Intelligence, Critical Infrastructure
Deep Learning, Forensics, Reverse Engineering
Law Enforcement, Cybercrime, Real World Threats, Policy, Data Privacy
Incident Response, Emerging Threat, SOC, Vulnerability, Security Development Life Cycle
Hosted By James Deakin
| 8:00 |
Registration |
|||
| 9:00 |
Opening Performance by Jake Juleous, Show Violinist |
|||
| WELCOME, KEYNOTE, AND PLENARY | ||||
|---|---|---|---|---|
| Rizal Ballroom | ||||
| 9:10 |
Martin Roesler IT Security in a Connected World Senior Director, Forward Looking Threat Research Trend Micro |
|||
| 9:35 |
Andrew MacPherson From Breach to Bust: A Short Story of Graphing and Grey Data |
|||
| 10:00 |
Stefano Zanero Securing Cyber-Physical Systems: Moving Beyond Fear Professor Politecnico di Milano |
|||
| 10:20 |
BREAK |
|||
| 10:40 |
Philip Casanova FSI Cybersecurity Concerns Vice President & CISO Maybank Philippines and New York |
|||
| 11:05 |
Marcelo de Azambuja Fortes A Global Effort to Fight Cybercrime Digital Crime Officer, Cybercrime Directorate Interpol |
|||
| 11:30 |
Jay Yaneza When Less is Really More: Integrated Intelligence When Analyzing Threats Senior Manager, Managed Detection and Response Trend Micro |
|||
| 11:50 |
LUNCH BREAK |
|||
| TRACK SESSIONS | ||||
| Man & Machine | Deeper Than Deep | Take Control | Offense Defense | |
Makati AB |
Manila AB |
Isabela A |
Isabela B |
|
| 13:00 |
A Look at Trends, A Glimpse of Insight |
ML-Boosted Massive Malware Processing* |
E-Shopping Fraud, The View From Cybercriminals Step-by-Step Guides and Underground Discussions |
Still Has a Lot To Learn: Bypassing Machine Learning AV Solutions |
| 13:35 |
The Role of AI and Machine Learning in Cyber Security |
Visual and Generative Malware Outbreak Detection |
(Picture of) Crouching Tiger, Hidden Malware |
N-Day Vulnerability Research: Denying Attackers Their Low-Hanging Fruit* |
| 14:10 |
IoT Malware Beasts and Where to Find Them |
Shifting Malware Technologies |
Password Security, Psychology, Smartness, and Gigabytes of Hashes: Results and Experience from and Organization-Wide Password Analysis |
100 0-days in 30 Minutes* |
| 14:40 |
BREAK |
|||
| 15:00 |
Discovering Exposed IoT Systems Using Commercial Feeds and Image Analysis Techniques |
Nor-Malfunction: The power hiDDEn within |
More Than Protection: Working with Law Enforcement to Disrupt Cybercrime* |
Looking Beyond the Hashes: Understanding Campaigns and Criminal Underground |
| 15:35 |
Seeing is Believing? How to Secure Your Wireless Horizon* |
Deep Learning: RNNs and Adversarial Examples |
Behind Every Big Attack is an Employee Who Opened an Email |
Security Operations Center in a Consumer Home Network |
| 16:10 |
CLOSING, RAFFLE |
|||

Host

Show Violinist